 I’m currently at the Parental Controls & Metered Data hackfest at Red Hat’s office in London. A bunch of GNOME people from various companies (Canonical, Endless, elementary, and Red Hat) have gathered to work out a plan to start implementing these two features in GNOME. The first two days have been dedicated to the parental control features. This is the ability for parents to control what children can do on the computer. For example, locking down access to certain applications or websites.
I’m currently at the Parental Controls & Metered Data hackfest at Red Hat’s office in London. A bunch of GNOME people from various companies (Canonical, Endless, elementary, and Red Hat) have gathered to work out a plan to start implementing these two features in GNOME. The first two days have been dedicated to the parental control features. This is the ability for parents to control what children can do on the computer. For example, locking down access to certain applications or websites.
Day one began with presentations of the Endless OS implementation by Philip, followed by a demonstration of the Elementary version by Cassidy. Elementary were interested in potentially expanding this feature set to include something like Digital Wellbeing – we explored the distinction between this and parental controls. It turns out that these features are relatively similar – the main differences are whether you are applying restrictions to yourself or to someone else, and whether you have the ability to lift/ignore the restrictions. We’ve started talking about the latter of these as “speed bumps”: you can always undo your own restrictions, so the interventions from the OS should be intended to nudge you towards the right behaviour.
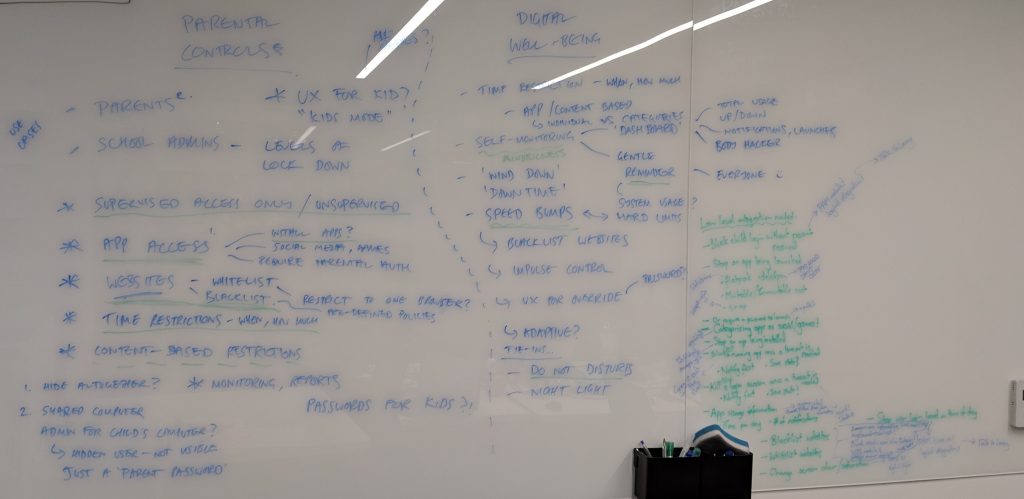
After that we looked at some prior art (Android, iOS), and started to take the large list of potential features (in the image above) down to the ones we thought might be feasible to implement. Throughout all of this, one topic we kept coming back to was app lockdown. It’s reasonably simple to see how this could be applied to containerised 📦 apps (e.g. Snap or Flatpak), but system applications that come from a deb or an rpm are much more difficult. It would probably be possible – but still difficult – to use an LSM like AppArmor or SELinux to do this by denying execute access to the application’s binary. One obvious problem with that is that GNOME doesn’t require one of these and different distributions have made different choices here… Another tricky topic is how to implement website white/blacklisting in a robust way. We discussed using DNS (systemd-resolved?) and ip/nftables implementations, but it might turn out that the most feasible way is to use a browser extension for this.
Adam Bieńkowski joined us to discuss the technical details of Elementary’s implementation and some potential ideas for future improvements there. Thanks for that!
Today we’ve spent a fair bit of time discussing the technical details about how some of this might be implemented. Given that this is about locking down other users’ accounts, the data ought to be stored somewhere at the system level – both so the admin can query/set it, and so that the user can’t modify it. Endless’s current implementation stores this in AccountsService, which feels reasonable to us, but doesn’t extend well to storing the information required to implement activity tracking. Georges and Florian have been discussing writing a system daemon to do this, which the shell and (maybe) browser(s) would feed into.
More detailed notes taken by Philip are available here.
For the next two days we will move to talking about the second subject for this hackfest – data metering.
Have you looked at pluckeye http://www.pluckeye.net/?
It’s really the only “Digital Wellbeing” app that actually works. It has a great “delay” feature and it’s really hard to circumvent. Nothing comes remotely close.
Being a cross-platform program, Pluckeye relies on obfuscation (the user can’t stop it without great effort). Windows and Mac OS do not allow any other way to “lock yourself out”, except crating a second admin account and “forgetting” your password, then writing a cron job to lock yourself out of your main admin account temporarily. This is quite a hassle and also risky. So pluckey just relies on obfuscation. While highly effective, it’s not a clean solution by any means.
But on Linux, it should be possible to create a “non-root” root with AppArmor and SELinux, an account that would control virtually everything EXCEPT the distraction blocker. You’d still need to “lose” your root-root password, but at least you’d have a functioning admin account at all times.
If this sounds interesting to you, please contact the pluckeye team through https://www.reddit.com/r/pluckeye/ or their main website (I am not affiliated). If you’re not sure, please contact them for details about their project anyway. Pluckeye has very few developer resources and if others got involved, it would be a huge help to their very important project.
An iron-clad distraction blocker could really be a huge selling point for desktop linux. It’s really a life-changing feature that no platform has successfully implemented yet.